Why is Exclusive Or (XOR) Important in Cryptography?
If you are getting into cryptography, or just trying to understand the fundamentals, you may have noticed that the exclusive or (XOR) operation is used quite often, especially in ciphers. XOR is a simple bitwise operation that allows cryptographers to create strong encryption systems, and consequently is a fundamental building block of practically all modern ciphers. Let’s dive into the details and see what makes XOR so important.
What is XOR?
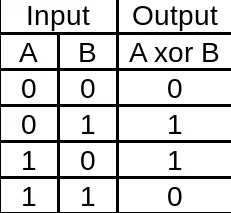
XOR, or “exclusive or” operates on binary data. It returns true if both of its inputs are opposites (one false and one true), otherwise, it returns false. You may see the operator written this way: ⊕.
For example, in Go, the code would be something like:
func exclusiveOr(a bool, b bool) bool {
return a != b
}
XOR Cipher - The Perfect Cipher
It is interesting to note that if:
- The key is the same size as the message
- The key is kept secret and generated truly randomly
Then the XOR cipher is certainly impossible to crack. This is known as a one-time pad. However, a simple XOR shouldn’t be used in production due to the key length needing to be too long to be practical.
Cipher Example
For instance, let’s simply encrypt the word “hi”
- First, convert “hi” to binary, here is a free tool)
01101000 01101001
- Next, create a random secret key that has the same length:
01010010 01000101
- Then, create an encrypted message by XOR’ing the message and the key:
01101000 01101001 ("hi")
XOR
01010010 01000101 (secret key)
=
00111010 00101100 (encrypted message)
- Finally, decrypt the message by XOR’ing the key with the encrypted message again:
00111010 00101100 (encrypted message)
XOR
01010010 01000101 (secret key)
=
01101000 01101001 ("hi")
Why does it work?
XOR works as a cipher because it is its own inverse.
𝑎 = (𝑎 ⊕ 𝑏) ⊕ 𝑏
And, as we demonstrated in our example:
encrypted = message ⊕ key
and
message = encrypted ⊕ key
Is XOR used in production ciphers?
The simple XOR cipher isn’t used in production because it is impractical to use keys that are the same length as the message body. However, the XOR is still extremely useful. In fact, it is used in almost all symmetric encryption algorithms. XOR is the primary operation in the “add round key” step of AES-256. It is also used in the DES cipher.
Related Articles
(Very) Basic Intro to Hash Functions (SHA-256, MD5, etc)
Jan 01, 2020 by Lane Wagner - Boot.dev co-founder and backend engineer
Hash functions are used to securely store passwords, find duplicate records, quickly store and retrieve data, among other useful computational tasks. As a practical example, all user passwords on boot.dev are hashed using Bcrypt to ensure that if an attacker were ever to gain access to our database our user’s passwords wouldn’t be compromised.
Cryptology vs Cryptography - Definitions and Differences
Dec 16, 2019 by Lane Wagner - Boot.dev co-founder and backend engineer
Many new developers are jumping right into writing code, usually for those fat paychecks, without learning much about the history of Computer Science. Alan Turing is recognized as the father of Computer Science, though many don’t know that his roots were in cryptology and mathematics. It was out of cryptology, cryptography, and mathematics that computer science was born.
Encoding vs Encryption - They Aren't the Same
Aug 14, 2019 by Lane Wagner - Boot.dev co-founder and backend engineer
While encryption does involve various methods of encoding data, the two are absolutely not interchangeable. In fact, if you get them mixed up it can result in serious data breaches and security vulnerabilities.